Microsoft Defender for Cloud Apps is a Cloud Access Security Broker (CASB) that supports various deployment modes, such as log collection, API connectors, and reverse proxy. It provides rich visibility, control over data travel, and sophisticated analytics to identify and combat cyber threats across all your Microsoft and third-party cloud services.
This document describes the steps to integrate Microsoft Defender for Cloud Apps with your WatchGuard Firebox.
Contents
Platform and Software
The hardware and software used to complete the steps outlined in this document include:
- Microsoft Defender for Cloud Apps
- WatchGuard Firebox
- Fireware v12.10
Test Topology

Set Up Microsoft Defender for Cloud Apps
Microsoft Defender for Cloud Apps is now part of Microsoft 365 Defender, which correlates singles from across the Microsoft Defender suite and provides incident-level detection, investigation, and powerful response capability. It is a comprehensive cross-SaaS solution bringing deep visibility, strong data controls, and enhanced threat protection to your cloud apps.
- Log in to the Microsoft 365 Defender portal.
- Select Settings > Cloud Apps.
- Under Cloud Discovery, select Automatic log upload > Data Sources.
- Click Add data source....

- In the Name text box, type the data source name.
- From the Source drop-down list, select WatchGuard XTM.
- Click View sample of expected log file > Download sample log. Make sure that the downloaded sample log matches your log files.
- From the Receiver type drop-down list, select Syslog - UDP.
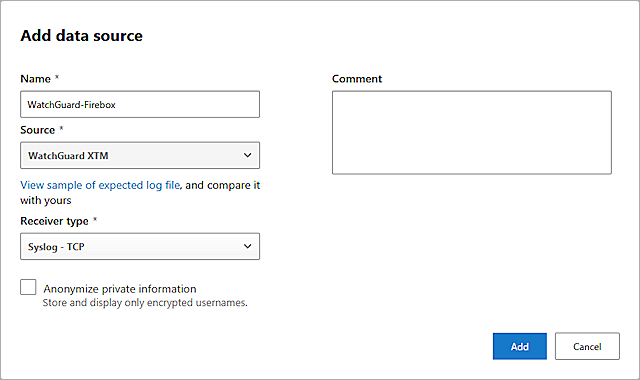
- Click Add.
- Select the Log collectors tab.
- Click Add log collector....
- In the Name text box, type the log collector name.
- In the Host IP address or FQDN text box, type the log collector server IP address.
- In the Data source(s) text box, select the data source you added.
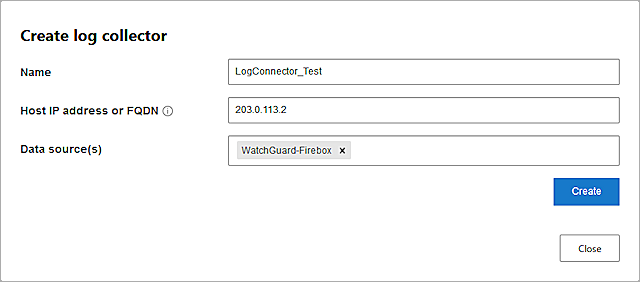
- Click Create.
- Follow the guide to deploy the log collector server.
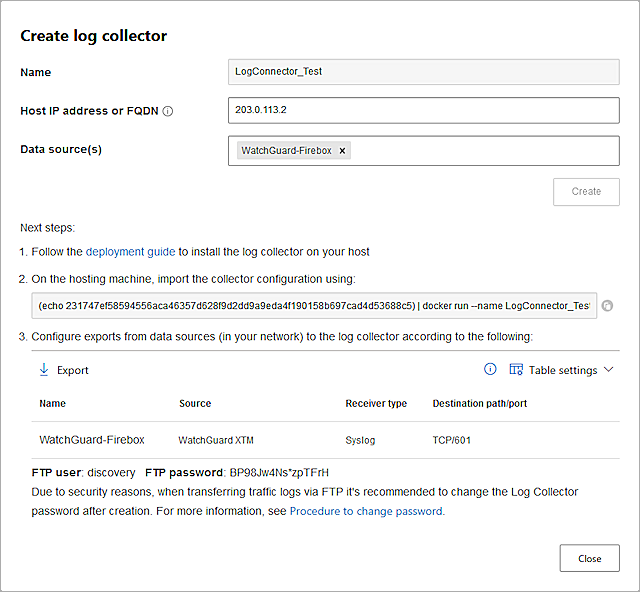
- Click Close.
Set Up Firebox
Complete the steps in this section to set up your Firebox.
Add a Syslog Server
- Log in to Fireware Web UI (https://<your firebox IP address>:8080).
- Select System > Logging.
The Logging page opens. - Select the Syslog Server tab.
- Select the Send log messages to these syslog servers check box.
- Click Add.
The Syslog Server dialog box opens. - In the IP Address text box, type the IP address of your log collector server.
- In the Port text box, type 514.
- From the Log Format drop-down list, select IBM LEEF.
- Do not change the default values for the other Syslog Server settings.
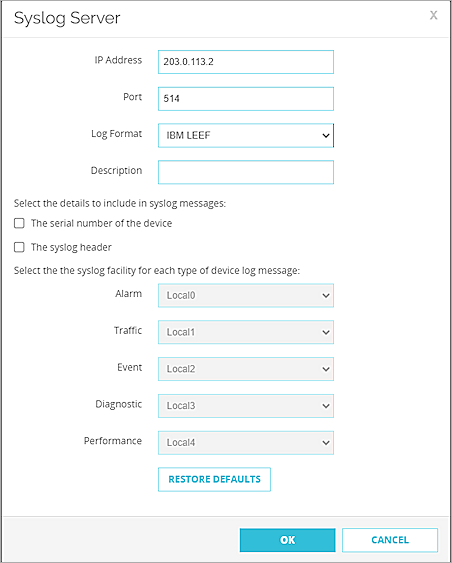
- Click OK.
- Click Save.
Add a proxy policies
When you add a proxy policy to your Firebox configuration file, you specify types of content that the Firebox must find as it examines network traffic. If the content matches (or does not match) the criteria you set in the proxy definition, the traffic is either allowed or denied, based on the criteria and settings you specify. In this example, we add a HTTPS-Proxy Policy with HTTPS-Client.Standard action.
- In the default firewall state, with no proxy policies and no traffic through the Firebox, you might see the message "Failed, Log format does not match the expected format for WATCHGUARD_XTM_SYSLOG" in the governance log. You can ignore this message.
- Verify your log format to make sure that it is formatted properly based on the sample log downloaded from Microsoft Defender for Cloud Apps.

-
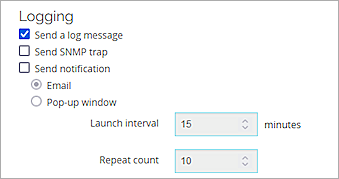
Make sure you select Send a log message when you want the Firebox to generate a log for an event.
Test the Integration
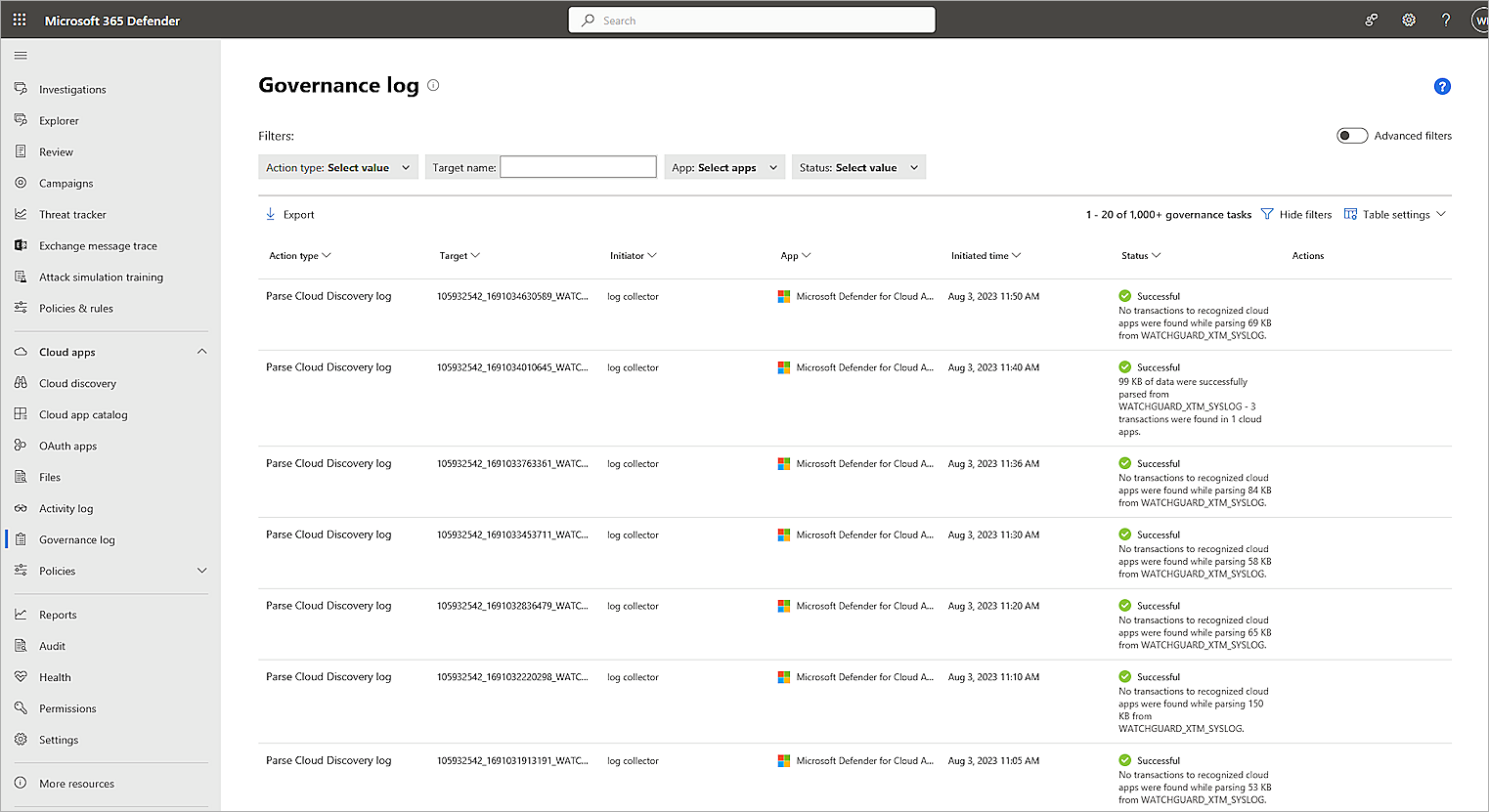
- Log in to Microsoft 365 Defender portal.
- Select Cloud apps > Governance log.
- Confirm the status for the Parse Cloud Discovery log is Successful.
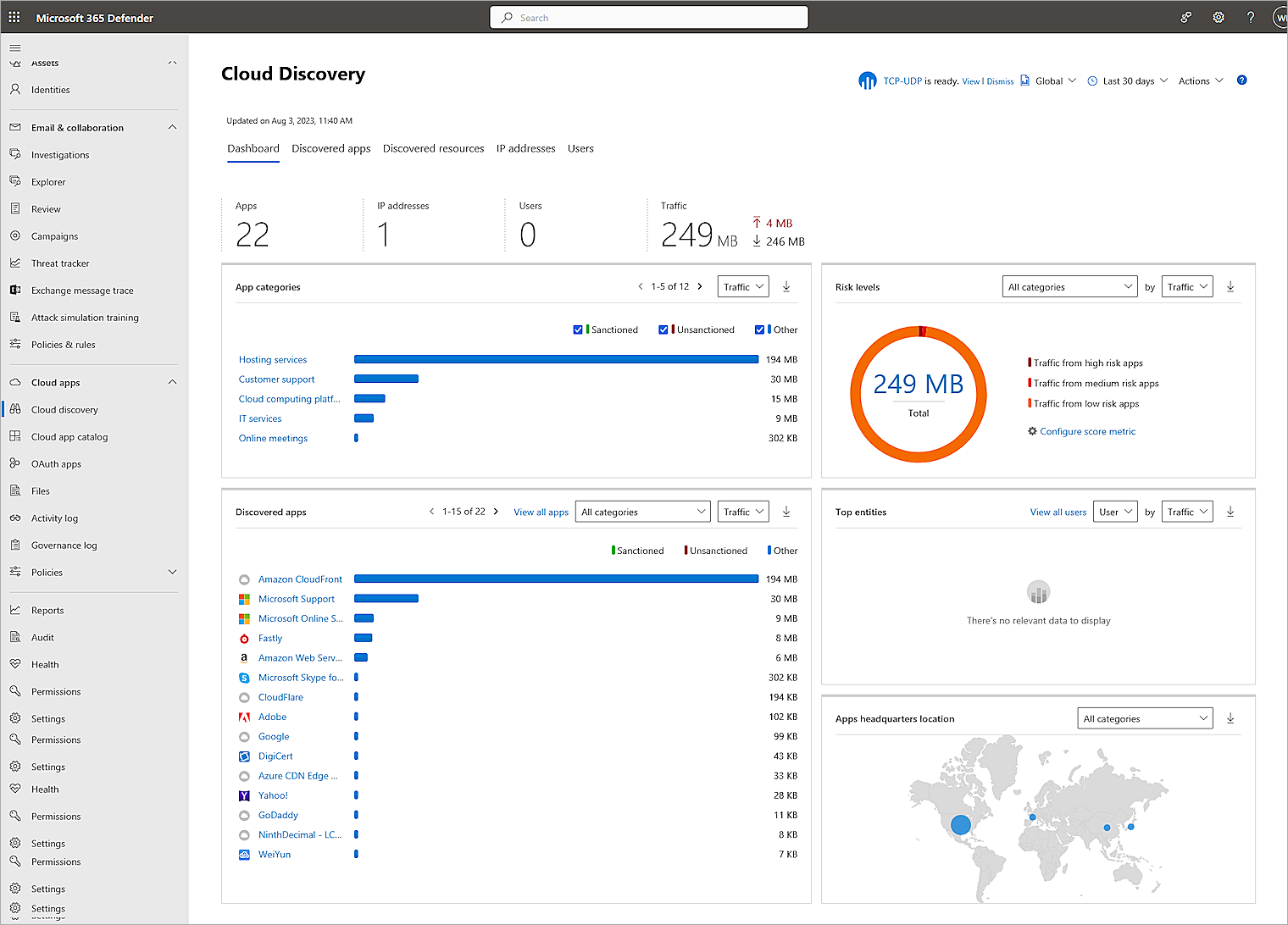
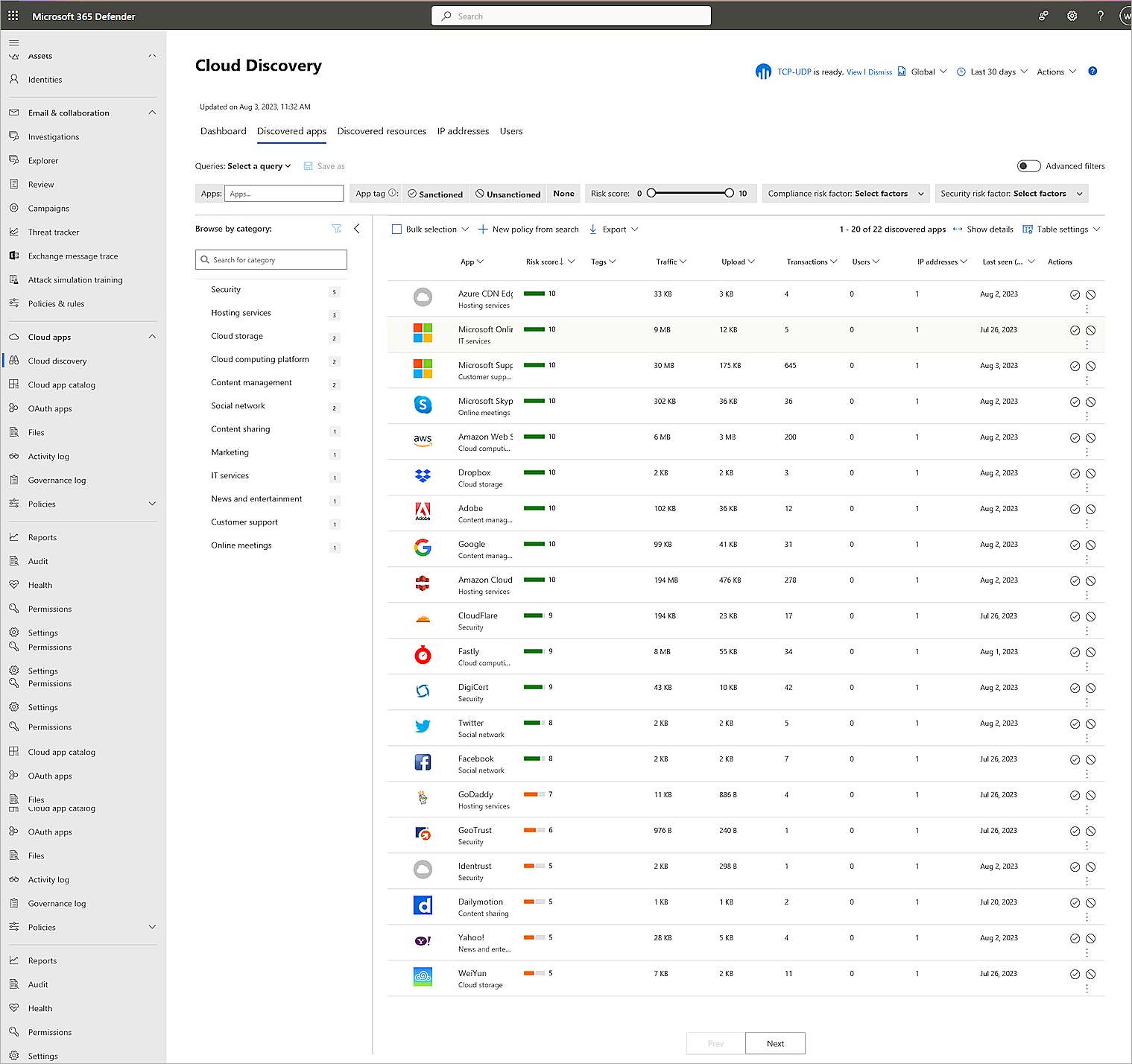
- Select Cloud apps > Cloud Discovery.
- Confirm the integration was successful.